Looking back at a year 2017 brings the internal conflict of being a security researcher into full view. On the one hand, each new event is an exciting new research avenue but at same time what were once theoretical problems find palpable expression in reality. This was a way to understand the actual attack surface and attacker tactics and to configure our systems hunt, detect and address new attacks. On the other hand, as people with concern for their network security posture of users at large, each event is a bigger catastrophe. Our predictions are an attempt to bring the form of trends likely to peak in the coming year.
High-end Mobile Malware.
 In August 2016, Pegasus, a so-called ‘lawful interception’ software suite, is sold to governments and other entities by an Israeli company called NSO Group. When combined with zero-days capable of remotely bypassing a modern mobile operating systems’ security defenses, such as iOS, this is a highly potent system against which there is little defense. In April 2017, Google published its analysis of the Android version of the Pegasus spyware which it called Chrysaor. In addition to ‘lawful surveillance’ spyware such as Pegasus and Chrysaor, many other APT groups have developed their own mobile malware implants.
In August 2016, Pegasus, a so-called ‘lawful interception’ software suite, is sold to governments and other entities by an Israeli company called NSO Group. When combined with zero-days capable of remotely bypassing a modern mobile operating systems’ security defenses, such as iOS, this is a highly potent system against which there is little defense. In April 2017, Google published its analysis of the Android version of the Pegasus spyware which it called Chrysaor. In addition to ‘lawful surveillance’ spyware such as Pegasus and Chrysaor, many other APT groups have developed their own mobile malware implants.
Due to the fact that iOS is an operating system locked down from introspection, there is very little that a user can do to check if their phone is infected. Total number of mobile malware existing in the wild is likely higher than currently reported, due to shortcomings in telemetry that makes these more difficult to spot and eradicate. In 2018 more high-end APT malware for mobile will be discovered, as a result of both an increase in the attacks and improvement in security technologies designed to catch them.
UEFI and BIOS attacks.
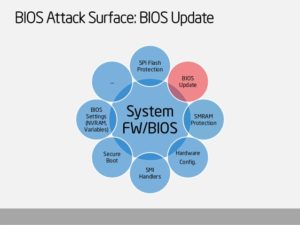 The Unified Extensible Firmware Interface (UEFI) is a software interface which serves as the intermediary between the firmware and the operating system on modern PCs. Established in 2005 by an alliance of leading software and hardware developers, Intel most notable amongst them; it’s now quickly superseding the legacy BIOS standard. This was achieved thanks to a number of advanced features that BIOS lacks: for example, the ability to install and run executables, networking and Internet capabilities, cryptography, CPU-independent architecture and drivers, etc. The very advanced capabilities that make UEFI such an attractive platform also open the way to new vulnerabilities that didn’t exist in the age of the more rigid BIOS. For example, the ability to run custom executable modules makes it possible to create malware that would be launched by UEFI directly before any anti-malware solution. The fact that commercial-grade UEFI malware exists has been known since 2015, when the Hacking team UEFI modules were discovered. With that in mind, it is perhaps surprising that no significant UEFI malware has been found, a fact that we attribute to the difficulty in detecting these in a reliable way. Again in 2018 we will see the discovery of more UEFI-based malware.
The Unified Extensible Firmware Interface (UEFI) is a software interface which serves as the intermediary between the firmware and the operating system on modern PCs. Established in 2005 by an alliance of leading software and hardware developers, Intel most notable amongst them; it’s now quickly superseding the legacy BIOS standard. This was achieved thanks to a number of advanced features that BIOS lacks: for example, the ability to install and run executables, networking and Internet capabilities, cryptography, CPU-independent architecture and drivers, etc. The very advanced capabilities that make UEFI such an attractive platform also open the way to new vulnerabilities that didn’t exist in the age of the more rigid BIOS. For example, the ability to run custom executable modules makes it possible to create malware that would be launched by UEFI directly before any anti-malware solution. The fact that commercial-grade UEFI malware exists has been known since 2015, when the Hacking team UEFI modules were discovered. With that in mind, it is perhaps surprising that no significant UEFI malware has been found, a fact that we attribute to the difficulty in detecting these in a reliable way. Again in 2018 we will see the discovery of more UEFI-based malware.
Router and modem hacks.
 Another known area of vulnerability that has gone vastly ignored is that of routers and modems. Be they home or enterprise, these pieces of hardware are everywhere, they’re critically important to daily operations, and tend to run proprietary pieces of software that go unpatched and unwatched. At the end of the day routers and modems are Internet-facing by design and thereby sitting at a critical juncture for an attacker intent on gaining persistent and stealthy access to a network. At a time of increased interest in misdirection and false flags, this is no small feat. Greater scrutiny of these devices will inevitably yield some interesting findings.
Another known area of vulnerability that has gone vastly ignored is that of routers and modems. Be they home or enterprise, these pieces of hardware are everywhere, they’re critically important to daily operations, and tend to run proprietary pieces of software that go unpatched and unwatched. At the end of the day routers and modems are Internet-facing by design and thereby sitting at a critical juncture for an attacker intent on gaining persistent and stealthy access to a network. At a time of increased interest in misdirection and false flags, this is no small feat. Greater scrutiny of these devices will inevitably yield some interesting findings.
Cryptographic vulnerabilities
 Juniper Networks discovered two mysterious backdoors in their NetScreen firewalls. The most interesting of the two was an extremely subtle change of the constants used for the Dual_EC random number generator, which would allow a knowledgeable attacker to decrypt VPN traffic from NetScreen devices. The original Dual_EC algorithm was designed by the NSA and pushed through NIST. It appears that this different set of constants made some APT actor unhappy enough to merit hacking into Juniper and changing the constants to a set that they could control and leverage to decrypt VPN connections. Then there was a flaw in a cryptographic library used by Infineon in their hardware chips for generation of RSA primes. While the flaw appears to have been unintentional, it does leave the question open in regards to how secure are the underlying encryption technologies used in our everyday life, from smart cards, wireless networks or encrypted web traffic. In 2018, we predict that more severe cryptographic vulnerabilities will be found, be they in the standards themselves or the specific implementations.
Juniper Networks discovered two mysterious backdoors in their NetScreen firewalls. The most interesting of the two was an extremely subtle change of the constants used for the Dual_EC random number generator, which would allow a knowledgeable attacker to decrypt VPN traffic from NetScreen devices. The original Dual_EC algorithm was designed by the NSA and pushed through NIST. It appears that this different set of constants made some APT actor unhappy enough to merit hacking into Juniper and changing the constants to a set that they could control and leverage to decrypt VPN connections. Then there was a flaw in a cryptographic library used by Infineon in their hardware chips for generation of RSA primes. While the flaw appears to have been unintentional, it does leave the question open in regards to how secure are the underlying encryption technologies used in our everyday life, from smart cards, wireless networks or encrypted web traffic. In 2018, we predict that more severe cryptographic vulnerabilities will be found, be they in the standards themselves or the specific implementations.
Automotive attacks
 Apps mean new way for cybercriminals to inject virus and they are a growing every day. Smartphone apps, many introduced by car manufacturers, which owners can download to remotely unlock their cars, check the engine status or find its location. Research has already demonstrated proof of concepts of how such apps can be compromised. It will not be long before Trojanized apps appear that inject malware direct into the heart of an unsuspecting victim’s vehicle. We will see more of these kind of attacks in next few years.
Apps mean new way for cybercriminals to inject virus and they are a growing every day. Smartphone apps, many introduced by car manufacturers, which owners can download to remotely unlock their cars, check the engine status or find its location. Research has already demonstrated proof of concepts of how such apps can be compromised. It will not be long before Trojanized apps appear that inject malware direct into the heart of an unsuspecting victim’s vehicle. We will see more of these kind of attacks in next few years.
Medical equipment hi-jacking
 Attacks targeting medical equipment with the aim of extortion, malicious disruption or worse, will rise. The volume of specialist medical equipment connected to computer networks is increasing. Many such networks are private, but one external Internet connection can be enough for attackers to breach and spread their malware through the ‘closed’ network. Targeting equipment can disrupt care and prove fatal, so the likelihood of the medical facility paying up is very high.
Attacks targeting medical equipment with the aim of extortion, malicious disruption or worse, will rise. The volume of specialist medical equipment connected to computer networks is increasing. Many such networks are private, but one external Internet connection can be enough for attackers to breach and spread their malware through the ‘closed’ network. Targeting equipment can disrupt care and prove fatal, so the likelihood of the medical facility paying up is very high.

This is actually helpful, thanks.
It works really well for me
Thank you for the wonderful post
You are so interesting! I do not think I’ve
truly read through anything like that before. So nice to discover another person with a few unique thoughts on this issue.
Really.. thanks for starting this up. This web site is something that’s needed on the web, someone with some originality!
I like what you guys are up too. This type of clever
work and coverage! Keep up the great works guys I’ve you guys to my blogroll.